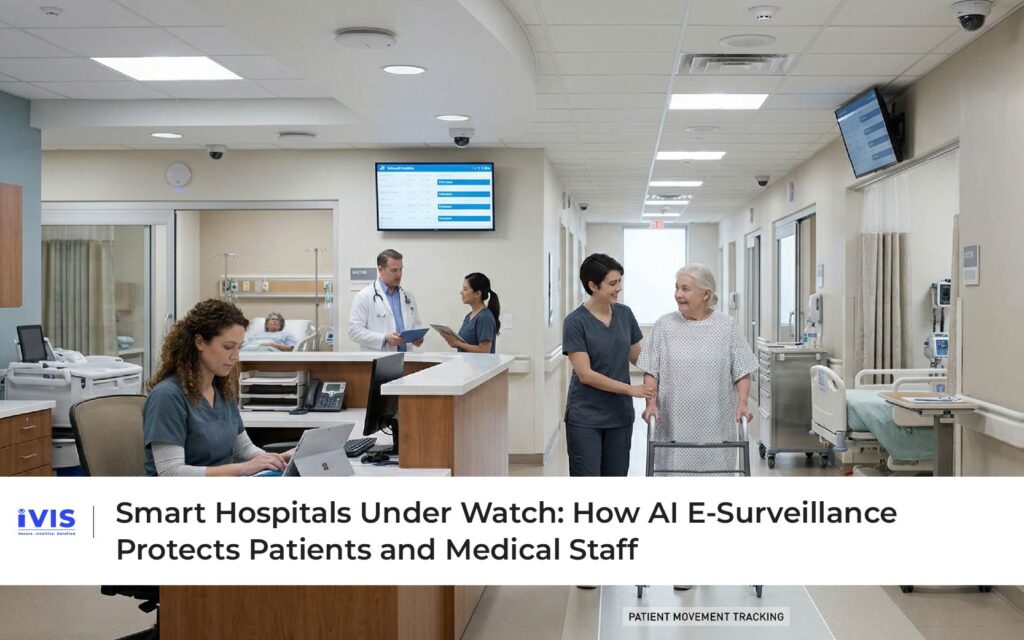
Smart Hospitals Under Watch: How AI Surveillance Protects Patients and Medical Staff
Smart Hospitals Under Watch: How AI E-Surveillance Protects Patients and Medical Staff Hospitals are among the most complex environments to manage. They operate 24/7, handle life-critical situations, and accommodate a constant flow of patients, caregivers, and visitors. Every second matters. Every decision carries weight. And every gap in visibility can have serious consequences. Traditionally, hospital safety has relied on a mix of human supervision, manual protocols, and basic CCTV systems. But as healthcare systems become more digitized and patient volumes increase, these approaches are no longer sufficient. Today, hospitals are evolving into smart, data-driven environments, where AI-powered e-surveillance plays a critical role in ensuring safety, efficiency, and compliance. From detecting patient falls to monitoring restricted zones and tracking high-value medical equipment, intelligent surveillance is transforming how hospitals protect both patients and staff. The Growing Need for Intelligent E-Surveillance in Healthcare Healthcare environments present unique safety challenges. Patients may be physically vulnerable, disoriented, or immobile. Staff operate under high stress and tight timelines. Equipment is expensive, mobile, and often critical to patient care. According to the World Health Organization (WHO), patient safety incidents are a leading cause of harm globally, with many incidents being preventable through better monitoring and timely intervention. Falls alone are among the most common adverse events in hospitals, particularly among elderly patients. At the same time, healthcare workers face occupational risks ranging from exposure to infectious materials to physical strain and workplace violence. Ensuring their safety is equally important for maintaining quality care delivery. These challenges demand systems that go beyond passive observation. Hospitals need real-time awareness and predictive insights, capabilities that AI-enabled e-surveillance can provide. From Cameras to Intelligence: The Evolution of Hospital E-Surveillance Traditional CCTV systems record events but rely on human operators to interpret them. In a busy hospital setting, constant manual monitoring is impractical and prone to oversight. AI-powered e-surveillance systems transform this model by embedding intelligence directly into video analytics. Instead of simply capturing footage, these systems analyze movement, behavior, and environmental conditions in real time. Machine learning models establish patterns of normal activity within specific hospital zones like in wards, corridors, ICUs, and operating rooms. When deviations occur, the system generates alerts that prompt immediate action. This shift from recording to interpreting is what makes modern e-surveillance a critical component of smart healthcare infrastructure. Fall Detection and Patient Monitoring One of the most impactful applications of AI surveillance in hospitals is patient fall detection. Falls can lead to serious injuries, prolonged hospital stays, and increased healthcare costs. AI-enabled systems analyze posture, movement patterns, and sudden changes in body position to detect potential falls in real time. Unlike wearable devices, which depend on patient compliance, video-based systems operate passively and continuously. Research published in IEEE on computer vision in healthcare indicates that AI-based fall detection systems can significantly improve response time compared to manual monitoring. Immediate alerts allow medical staff to intervene quickly, reducing the severity of injuries. Beyond falls, AI e-surveillance can monitor patient movement in high-risk wards, such as dementia units or post-operative recovery areas. If a patient leaves a designated safe zone or exhibits unusual behavior, staff are notified instantly. Protecting Medical Staff and Enhancing Workplace Safety Healthcare workers operate in environments where safety risks are both physical and biological. Monitoring staff safety is therefore essential. AI-powered e-surveillance systems can detect overcrowding in treatment areas, monitor compliance with hygiene protocols, and identify unsafe conditions such as spills or obstructions in corridors. During infectious disease outbreaks, monitoring adherence to personal protective equipment (PPE) protocols becomes especially critical. The WHO emphasizes that improving healthcare worker safety directly enhances patient outcomes. By providing real-time visibility into operational conditions, intelligent surveillance helps hospitals maintain safer working environments. Additionally, e-surveillance systems can support incident documentation, providing clear records that help in resolving disputes or investigating workplace incidents. Equipment Tracking and Asset Management Hospitals rely on a wide range of medical equipment – ventilators, infusion pumps, diagnostic devices, many of which are mobile and in high demand. Misplaced or unavailable equipment can delay treatment and impact patient outcomes. AI-enabled e-surveillance systems can track the movement of critical assets across hospital premises, ensuring they are available where needed. By combining video analytics with location tracking technologies, hospitals can reduce equipment loss, optimize utilization, and improve operational efficiency. According to McKinsey’s research on healthcare operations, improved asset visibility can significantly reduce operational inefficiencies and costs in large medical facilities. Securing Restricted Zones and Sensitive Areas Hospitals contain multiple restricted areas, including operating rooms, pharmaceutical storage units, laboratories, and intensive care units. Unauthorized access to these zones can pose serious risks. AI-driven e-surveillance systems monitor access points and detect unusual activity in restricted areas. Behaviour-based analytics identify deviations such as loitering, unauthorized entry attempts, or unusual movement patterns. Unlike traditional access control systems that rely solely on credentials, AI e-surveillance provides contextual awareness, understanding not just who entered, but how they behaved within the space. This layered security approach enhances both safety and compliance with healthcare regulations. Enhancing Compliance and Audit Readiness Healthcare is one of the most regulated industries. Hospitals must adhere to strict standards related to patient safety, hygiene, data protection, and operational protocols. AI-powered e-surveillance supports compliance by providing continuous monitoring and verifiable evidence. Time-stamped video records, automated alerts, and detailed logs help hospitals demonstrate adherence to protocols during audits. Deloitte’s research on digital compliance highlights that real-time monitoring systems significantly improve audit readiness and reduce the risk of regulatory violations. In this context, e-surveillance becomes not just a safety tool, but a compliance enabler. The Role of IVIS in Smart Hospital E-Surveillance To manage the complexity of modern healthcare environments, hospitals require integrated platforms that unify e-surveillance, analytics, and operational workflows. This is where IVIS plays a significant role. IVIS enables hospitals to centralize surveillance across multiple departments and facilities, transforming video data into actionable intelligence. Through AI-powered video analytics, IVIS supports real-time detection of patient risks, staff safety issues, and operational anomalies. Its architecture allows for both edge-based processing, ensuring low-latency alerts and centralized dashboards for comprehensive oversight. Configurable workflows ensure that alerts are directed to the right personnel, enabling rapid response without disruption. Importantly, IVIS in collaboration with Scanalitix, incorporates robust data governance, access control, and audit capabilities, aligning hospital surveillance systems with regulatory and ethical requirements. In practice, IVIS helps healthcare institutions transition from reactive monitoring to proactive, intelligence-driven safety management. The Future of E-surveillance in Healthcare As hospitals continue